If you run an eCommerce store on PrestaShop, you’re probably aware that the latest version- PrestaShop 1.7.8.7- was released on 25 July 2022.
This update is particularly significant because it fixes several critical security issues that could allow an unauthorized user to access or modify data on your site. If you’re running PrestaShop 1.7.8.6, we recommend upgrading to 1.7.8.7 as soon as possible to take advantage of this security patch.
Like previous versions, this PrestaShop upgrade is recommended to keep your shop safe from attacks.
Let’s discuss more about it.
Where the Issue Lies?
PrestaShop Inc. has been powering eCommerce stores for years now. Unfortunately, some hostile performers exploit known and unknown security vulnerabilities to inject malicious code into PrestaShop websites, making them steal customers’ payment information.
Must Read: Why Hire Top PrestaShop Development Companies In 2023?
Who are Under Attack?
- PrestaShops that are vulnerable to SQL injection attacks.
- Online eCommerce store using outdated software or modules.
- PrestaShops that are using vulnerable third-party modules.

How Does the Attack Work?
Based on the conversations between the developers and the eCommerce owners, the systematic method of operation looks like this:
- The attacker makes a POST request to the endpoint vulnerable to SQL injection.
- A GET request to the homepage with no parameters is submitted within one second by the attacker. It results in a PHP file called blm.php at the root of the eCommerce directory.
- Finally, the attacker submits a GET request to the new file, blm.php, allowing them to perform random activities.
Fake payment forms are injected into the front-office checkout page, and the customers fill their credit card information on the artificial form, unknowingly sending it to the attackers.
How to Keep Your Online Business Safe?
Update to the Latest PrestaShop Version
Ensure that your PrestaShop is operating on the latest version and that your modules are updated. Thus, preventing your eCommerce from being exposed to known and actively exploited SQL injection vulnerabilities.
Disable MySQL Smarty cache
To break the attack chain, physically disabling the MySQL Smarty cache storage feature in the PrestaShop code is recommended.
Perform Regular Checks
Your store requires regular checks and security scans to identify and eliminate potential malicious codes, viruses, hidden spam links, and spam pages. It is vital to remove all sources of vulnerabilities for strengthened security.
Update to Strong Passwords Regularly
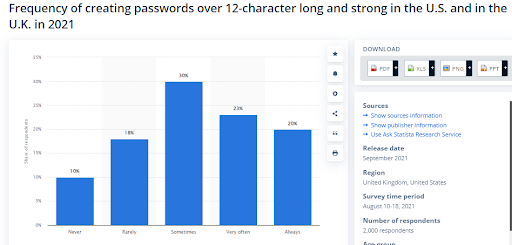
It might seem trivial, but updating to strong store passwords regularly acts as the first line of defense against various forms of hacking. Mandating strong passwords will become one of the standard web features in 2023.
Ensure SSL Certificate Integration
SSL stands for secure socket layer, and as the name suggests, it offers an added layer of security to websites, web apps, mobile apps, and other software. A site with SSL offers data encryption between the web server and user communication. This helps to secure sensitive data like credit card details, customer personal information, username, passwords, etc.
You can easily check whether your website has an SSL certificate or if you need to integrate one. Simply open the website over a browser. The website with SSL certificates showcases a green or black colored padlock icon in the address field right before the store address.
Bugs Fixed
- Strengthens the MySQL Smarty cache storage against code injection attacks.
- Security.
- Eval injection if the shop is vulnerable to an SQL injection.
Reminder: Keep your PrestaShop version updated to prevent such attacks. Don’t forget to regularly check for updates related to your PrestaShop software, modules, and server environment.
Must Read: PrestaShop 8.0: The Final Version Is Here!
Safest Approach to Upgrade Your PrestaShop
With these and many other changes, PrestaShop 1.7.8.7 is a must-have update.
Be aware that managing PrestaShop on your own can invite various bugs or technical issues! Consider contacting a specialist to perform a full audit of your PrestaShop and work on it.
Being a PrestaShop partner agency, we have certified PrestaShop experts on board who can help you upgrade/update to the latest version of PrestaShop,i.e., 1.7.8.7.
Let’s connect and get the needful done.

2500+
Project Launched
20+
Years of Experience
250+
Skilled Professionals
60+
Days of Free Support
Frequently Asked Questions
Q1. Why do you need PrestaShop login security?
PrestaShop login security with two-factor authentication (2FA) eliminates the risks associated with compromised passwords. Even if a user’s password has been hacked, guessed, or phished, the attacker fails to log in. Login is successful only after the approval of the second factor.
Q2. How to manually upgrade your PrestaShop?
Manual upgrade of a Prestashop store involves you implementing the following steps:
- Download PrestaShop’s latest version
- Go to the compressed archive and extract files
- Further, switch the store to the maintenance mode
- Disable caching
- Next, copy the files to the server
- Update your database
- Eliminate the “Install” folder
- Update forms
Q3. How to set up PrestaShop multistore?
To enable multiple stores in PrestaShop, you need to do the following:
- Navigate to the shop parameters
- Go to General
- Now enable the Multistore option
This creates a multishop tab under the advanced parameters section.

